OnlyFans downloader Chrome extensions that allow users to download OnlyFans videos often get removed quickly from the Chrome Web Store. This happens because downloading videos from OnlyFans is against their rules, even if you’re paying for the content.
But no need to worry; many aren’t aware that you can use almost any freely available video downloader extensions for the Chrome browser to easily save videos from OnlyFans. In this article, I have listed five such video downloader extensions for Chrome to seamlessly download videos from OnlyFans.
Note: After installing the extension, be sure to refresh the OnlyFans website. Then, play the video you wish to download so that the extension can capture it properly.
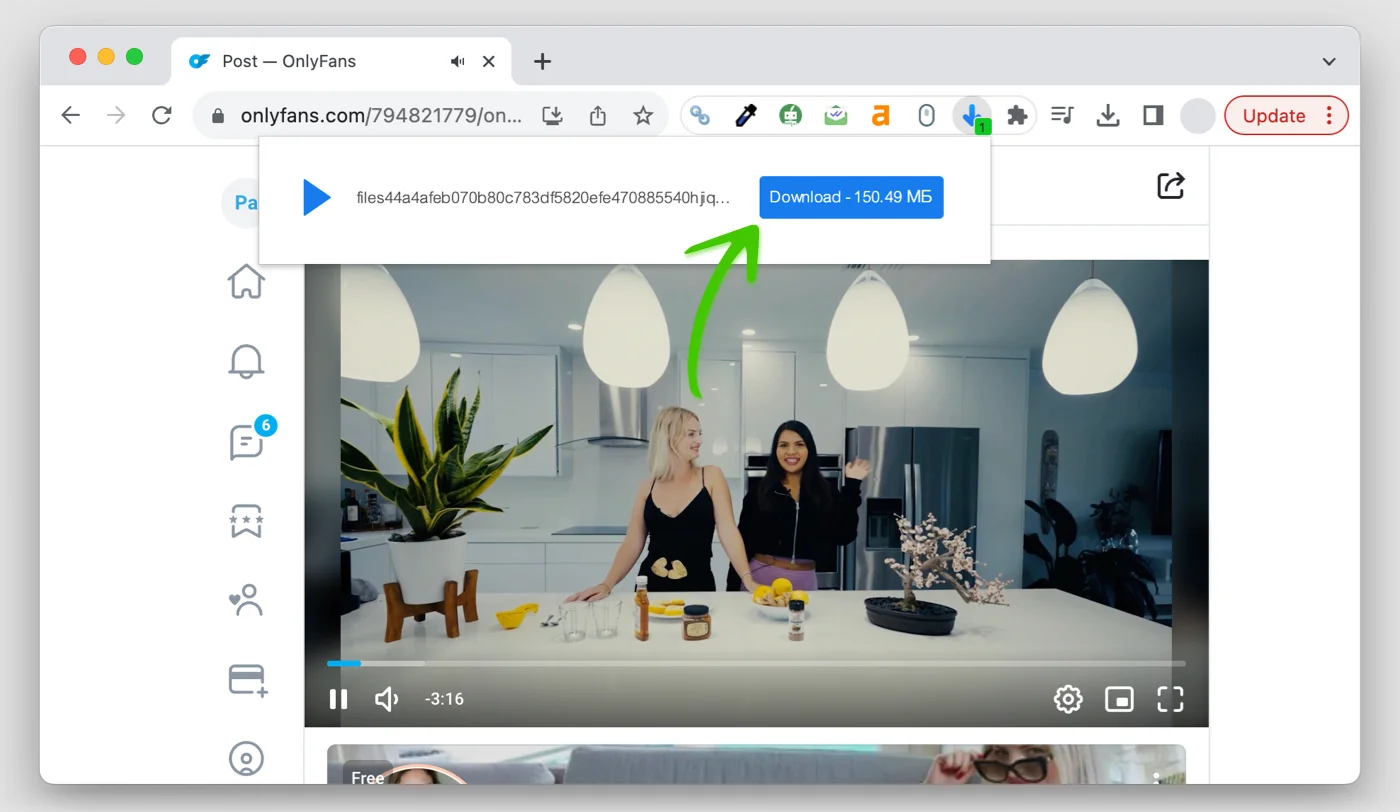
1. Video Downloader Online for OnlyFans
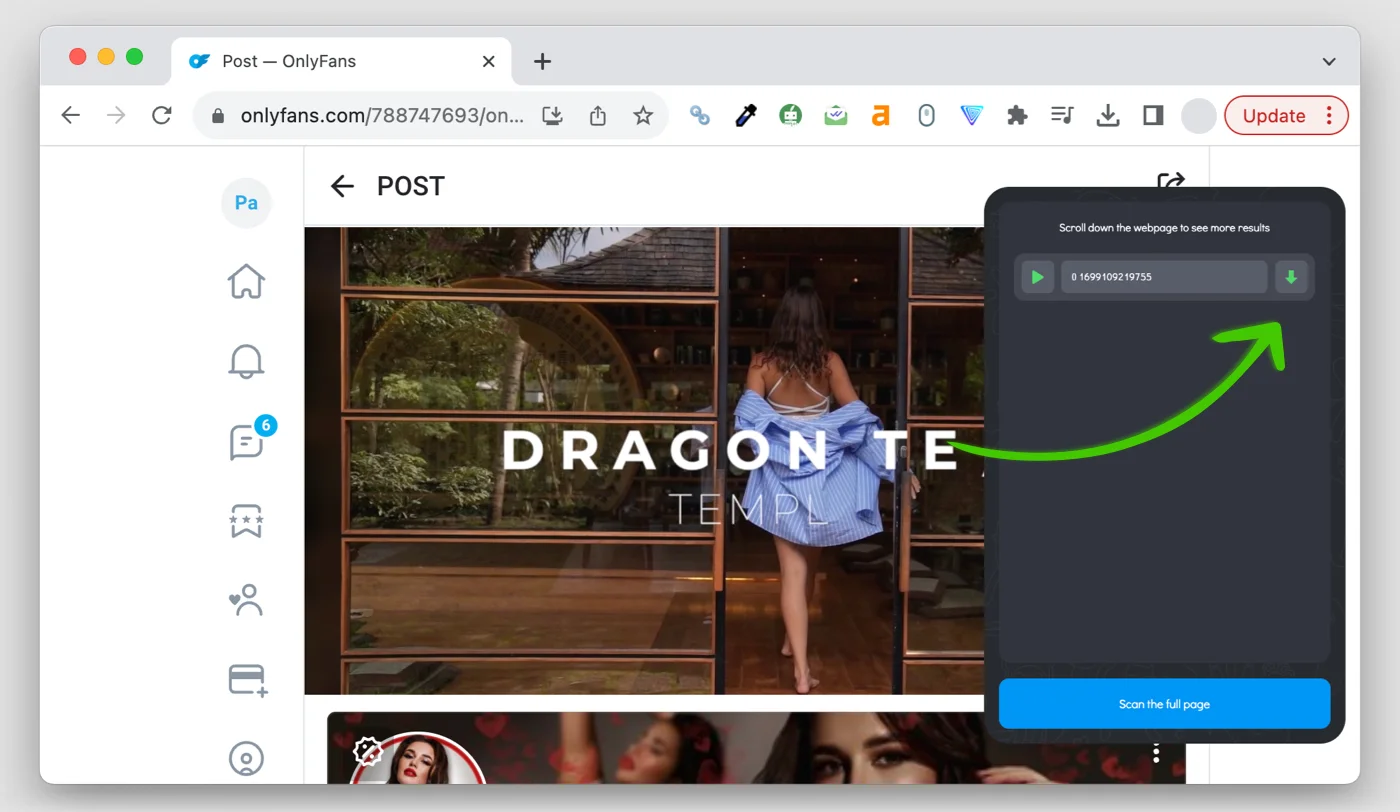
Video Downloader Online is a powerful and straightforward extension for Chrome that you’ve been looking for to download videos from OnlyFans. Effortlessly save your favorite videos in various formats like MP4, FLV, and MKV directly to your hard drive from almost any website. Check out the screenshot below:
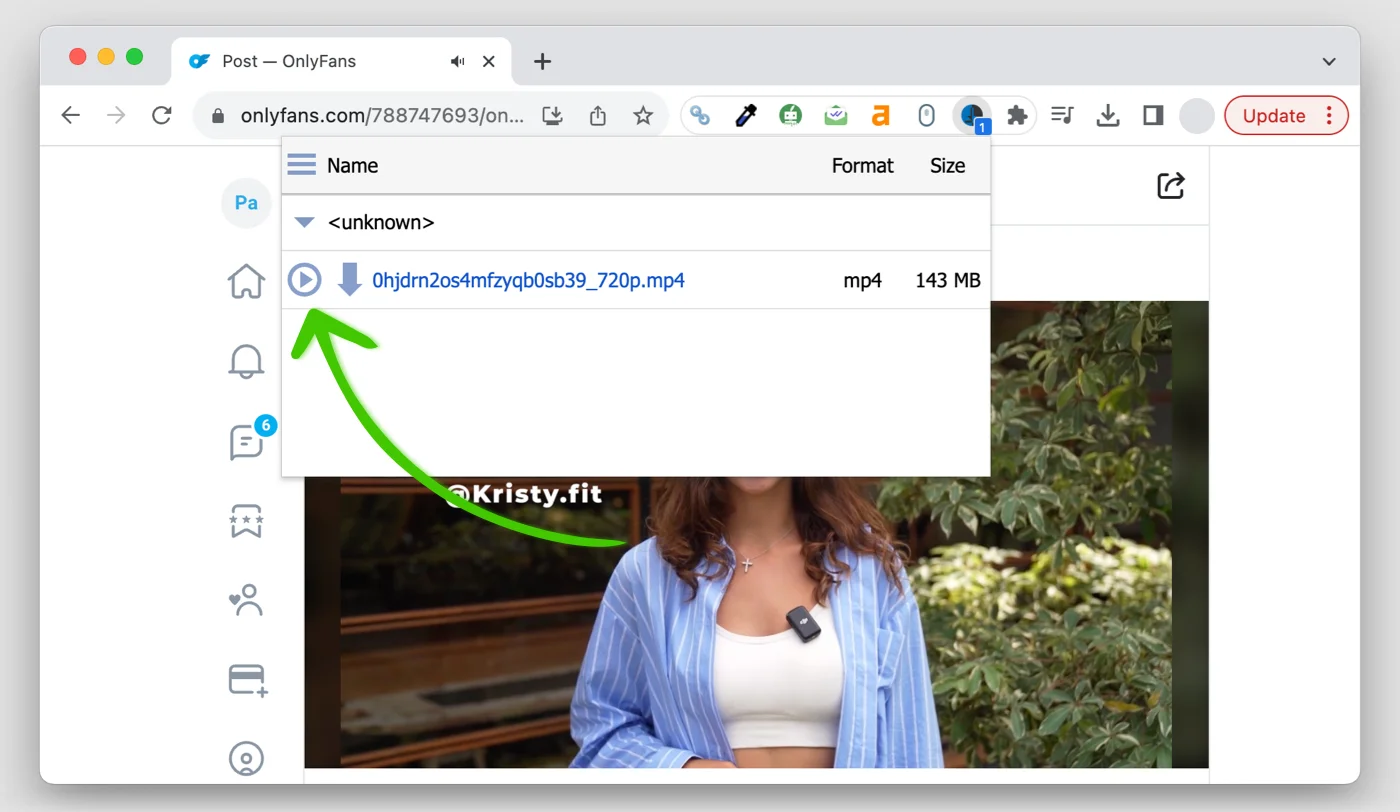
2. Video Downloader Pro for OnlyFans
Video Downloader Pro is your go-to Chrome extension for swiftly downloading videos from any web page, including OnlyFans. Just click the extension icon, select from the available files, and in moments, the video will be downloaded and saved to your computer.
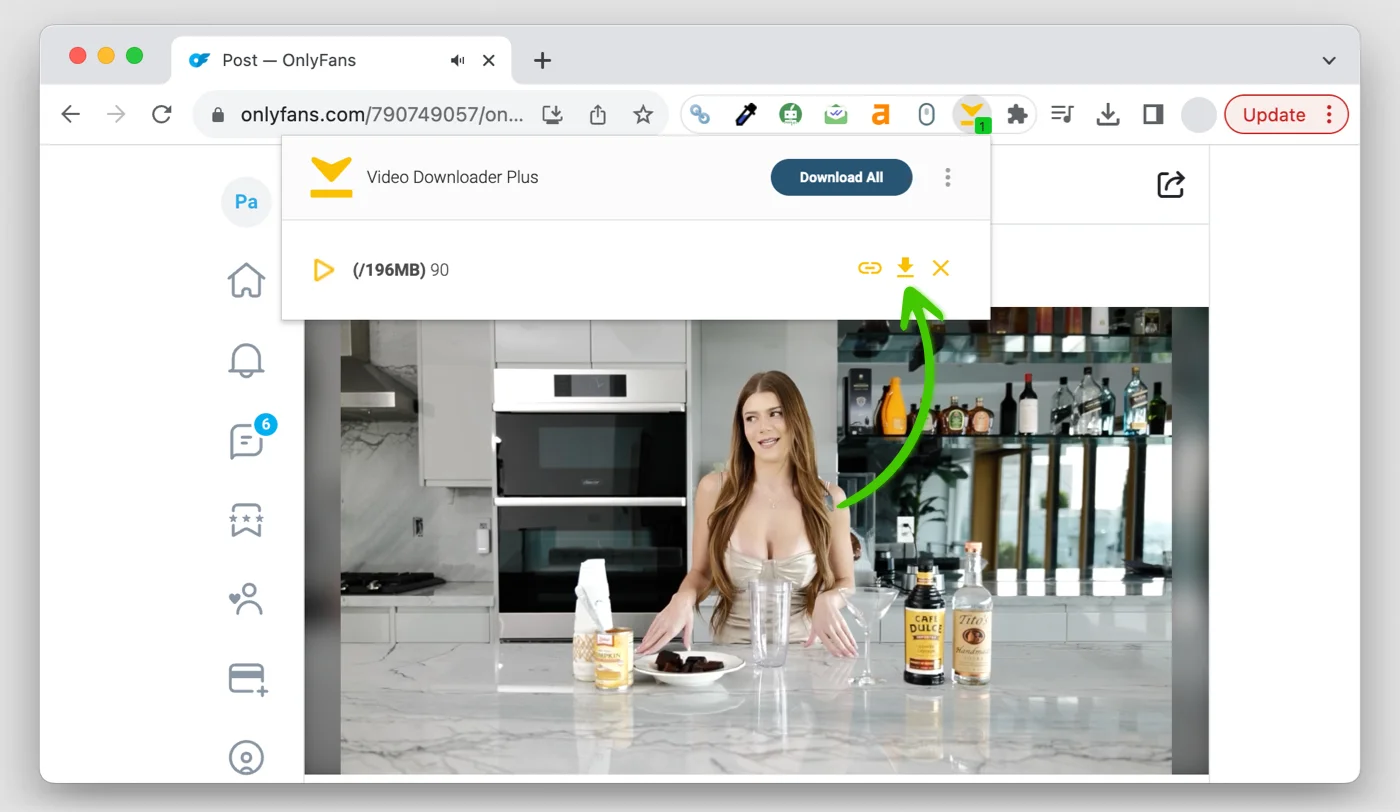
3. Video Downloader for OnlyFans
This simple Video Downloader Chrome extension effortlessly supports over 1,000 streaming platforms, such as OnlyFans, Instagram, TikTok, Vimeo, Dailymotion, and Facebook. It allows you to download music and video streams, full movies, and even entire videos from playlists and channels with ease.
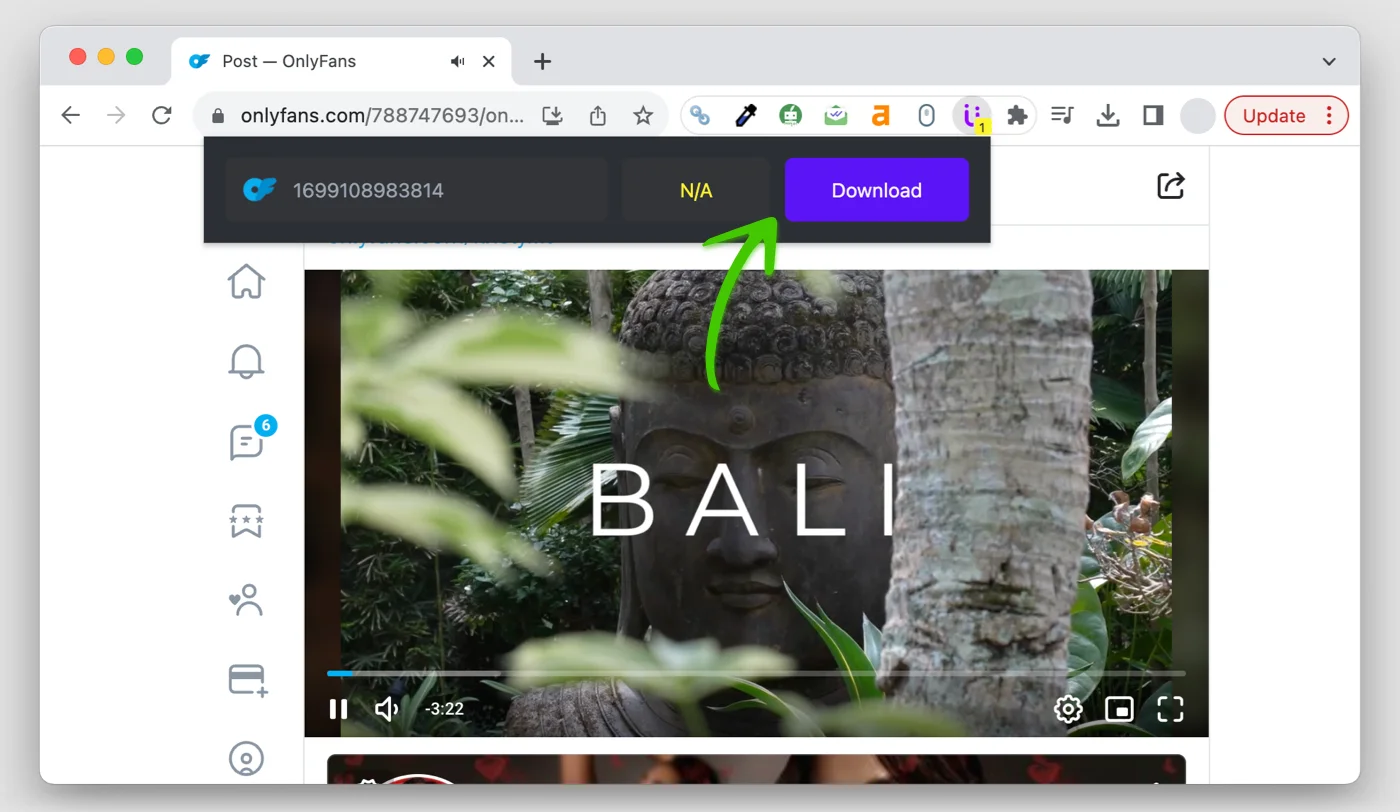
4. Video Downloader for U
The Video Downloader for U extension for Chrome enables quick and effortless saving of videos from multiple online sources. This user-friendly tool offers a swift solution for downloading videos, allowing you to enjoy them later, offline, and share memorable moments with friends. Safely store your downloaded videos on your PC to watch whenever you wish.
5. Video Downloader for Chrome
Video Downloader for Chrome streamlines the process of saving videos from various social media platforms, including OnlyFans. With a quick installation, it integrates a download button directly into your browser, simplifying the video-saving process. There’s no need to visit a different site; simply click the button, choose your desired format and quality, and download your video right from the source page.
To wrap up, while dedicated OnlyFans downloader extensions may face rapid removal from the Chrome Web Store due to policy violations, there are still a lot of general video downloader extensions that can serve the same purpose.
In this article, we have seen five such versatile Chrome extensions that can assist you in downloading content from OnlyFans with minimal fuss. Always remember to respect copyright and the terms of service of content platforms. These Chrome extensions are meant to provide a solution for those who wish to view their legally obtained content offline and should be used responsibly.
If you face any problems downloading OnlyFans videos or installing these Chrome extensions, do let us know, and I will try our best to help you out.
Related Posts:
- How to Download OnlyFans Videos in Microsoft Edge
- Download OnlyFans Videos using OnlyFans Downloaders
- 4 Ways to Download OnlyFans Videos in HD for Free
- How does OnlyFans Keep Content Secure
- The Risks of Downloading Torrents on Mac
- 10 Video Games With The Best Female Lead
