At Hacker9, we always advise our readers to be vigilant internet users, no matter how informed they are, and to keep up with the new tactics used by hackers to trick their victims.
Until this year, there have been numerous data breaches, which mostly started with a simple phishing attack. Hackers have targeted various financial accounts, looking for sensitive data, most of which use Office 365 and Google Workspace. Many times, these attacks come in the form of “security alerts” or “warning” messages.
Its 2019, and hackers have already raised their phishing game, coming up with new ingenious phishing attacks. Also, hackers are well aware that internet users are more informed about phishing attacks than ever.
A few days ago, we saw how 2-factor authentication codes can be bypassed easily using the phishing technique itself, and today we are going to cover two new phishing attack trends that even the most informed internet users could fall for.
Before that, let me list the basic security practices we recommend to spot a phishing site.
- Checking if the URL is correct
- Checking if the site is using HTTPS
- Checking if the website domain name is not a homograph
- Checking if the website’s domain name is not using Punycode
- Using a browser extension to detect phishing URLs
We should always rely on and follow the above-listed security practices to beat phishing attacks. However, you may still fall victim to the two newly discovered creative phishing attacks listed below.
Hiding Phishing URL Behind Google Translate
The modus operandi here is to hide the phishing page URL by masking it with the Web address of Google Translate service (translate.google.com) so that the users begin to feel that the page is the real one. This increases the chances of users falling for the trap as they see Google Domain at the top and gain confidence.
This trick looks less sophisticated, but sure, it is one of those clever tricks used by cybercriminals to hijack Google accounts.
The attack specifically targets Google account holders, specifically Google Workspace users, and is carried out by sending phishing emails with the subject line ‘Security Alert’ to a group of users to warn them of the unauthorized sign-in from another device.
The email contains very realistic Google warnings that you normally receive when you sign in or attempt to sign in to your account from an unauthorized or new device. Along with the warning text, there is a button with a link to the dubious website.
When you hesitantly click on the button, you are taken to the phishing site via the “Google translate service,” i.e., I.e the “Google translate service” fills up the phishing site URL with random text and displays Google’s legitimate domain.
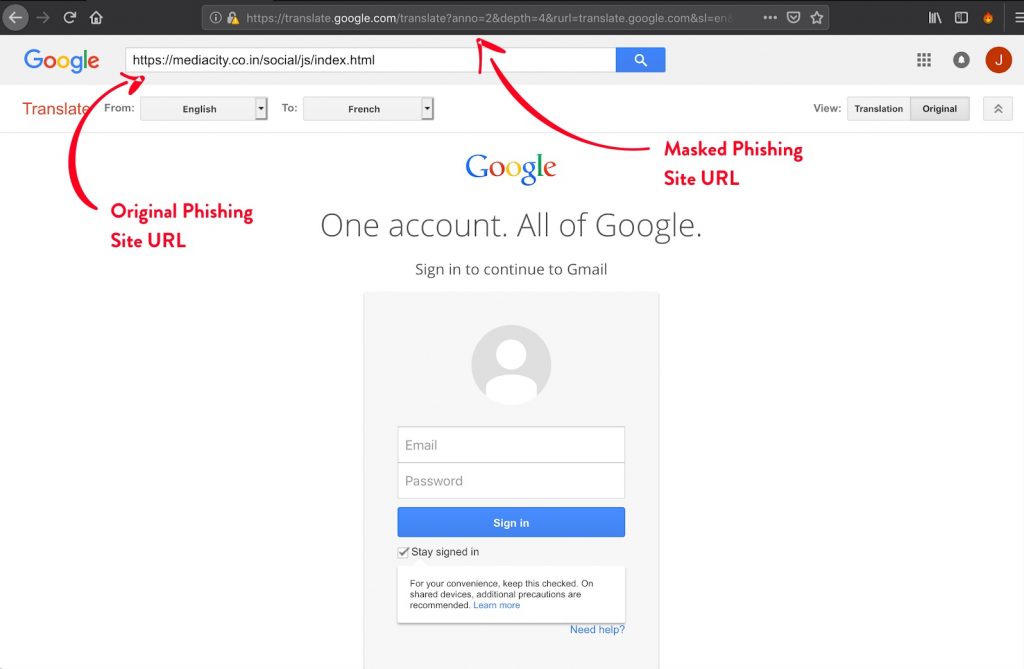
While on the desktop computer, there are enough signals to warn you about the hidden dangers, whereas if the victim happens to be on his mobile device, the attack becomes very lethal and is more difficult to spot since the URL is compressed enough to look authentic at first glance.
Signals like seeing the phishing URL in the Google Translate toolbar, hovering over the links inside the page, inspecting the page elements, etc. will easily tell you that something is fishy. However, if you are on your cellphone, it is quite difficult to spot the attack unless you care enough to observe the URL.
Using in-page fake Facebook login popup
Making use of the Facebook login option at various social networking websites is totally fine, and we have been using this option since its inception as an easy and effortless way of registering on 3rd party websites. It is needless to say that Facebook is well aware of how and where the Facebook login option is being used.
Generally, when you click the “log in with Facebook” option available on any website, you are served with facebook.com in a new pop-up browser window, asking you to enter your Facebook credentials to authenticate using OAuth and permitting the service to access your profile’s necessary information, like your email.
Antoine Vincent Jebara, CEO of Myki, says that his team recently spotted a new phishing attack campaign that even the most vigilant users could fall for.
Hackers are distributing links to blogs and services that prompt visitors to first “login using the Facebook account” to read an exclusive article or purchase a discounted product. The catch here is that the “login using Facebook account” option is rigged. Instead of being redirected to a real Facebook popup page, the users are being served with a very realistic-looking fake Facebook login prompt after they click the “login using Facebook account” button, which has been crafted to capture the user’s credentials, just like any phishing site.
The whole fake Facebook login popup is built with HTML and javascript within the original page itself, i.e., it is reproduced to look and feel exactly like a legitimate browser window, including a status bar, navigation bar, shadows, and URL to the Facebook website with a green lock pad indicating a valid HTTPS.
Watch the demonstration video that Myki shared:
As shown in the video, the users can also interact with the fake browser window, drag it here-and-there or exit it in the same way any legitimate window acts. The only thing that they can’t do is, drag the prompt away from or out of the window it is currently displayed in.
And according to Vincent, this is the only signal which tells you that the popup is fake, I.e If dragging the pop-up out of the window it is currently displayed-in fails, it’s a definite sign that the popup is fake. If you are a web developer, you could also inspect the HTML page elements to know the sources of its components.
Final word
Hackers are well aware of the fact that more of us are using mobile than ever before, and a more sophisticated hacker could clearly use the limitations of the mobile phone to take advantage. So you need to be very cautious about the websites you visit or maliciously intended emails you may fall for while on your mobile phone.
Related posts:
- How to track Facebook user location
- Facebook fake account finder
- How to trace a fake Facebook account
- How to find IP address from Facebook profile on android
- Easy way to hack Facebook account from mobile
- Facebook group invite all script
